Can an AI Write a Working Exploit?

Me and Rodrigo Laneth were having a discussion about how useful LLMs would actually be for cybersecurity research and pentesting. Not the “write me a fuzz harness” kind of useful – we were wondering if an LLM could go from a vulnerability description all the way to a working exploit PoC. Not just a crash, but actual RIP control. So we decided to test it. The AI Gatekeeping Problem If you’ve ever tried to use OpenAI or Anthropic for anything security-related, you know the drill. They just refuse. Rodrigo tried submitting the vulnerability details to both OpenAI Codex and Anthropic...
Reverse Engineering the AIR105 Bootrom - A Deep Dive into the MH1903S Boot Process
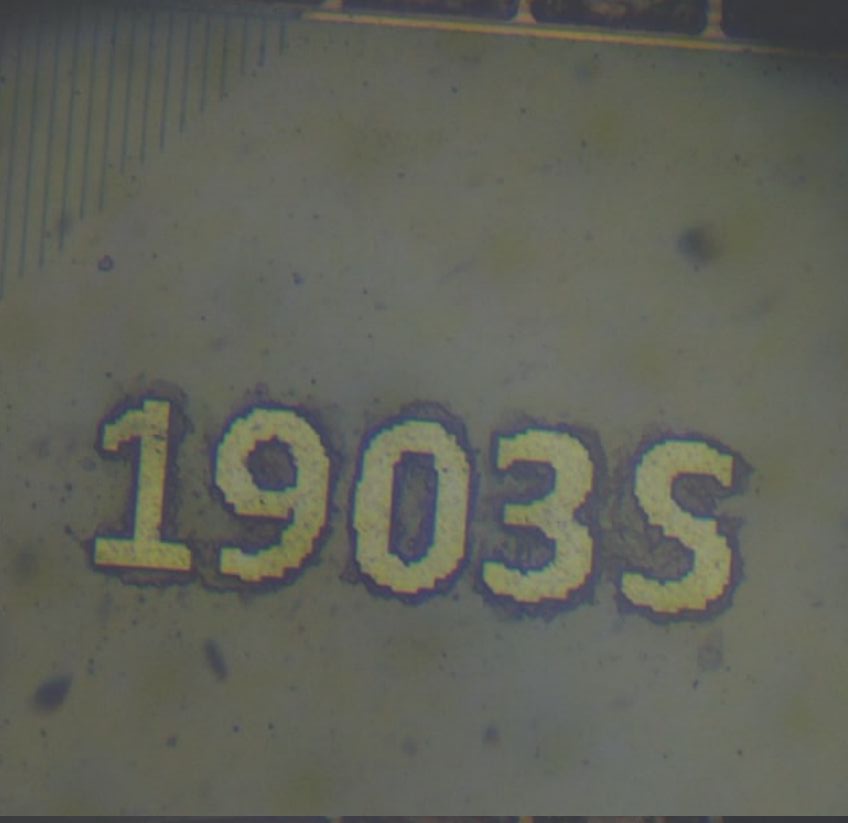
Reverse Engineering the AIR105 Bootrom: A Deep Dive into the MH1903S Boot Process The AIR105 is a secure microcontroller built around the MH1903S core — an ARM Cortex-M4F processor running at 168 MHz, designed for payment terminals and other security-critical embedded applications. It features hardware cryptography (SM2/SM3/SM4, AES, RSA-2048, SHA-256/384/512), OTP (One-Time Programmable) memory for key storage — though as we’ll see, the bootrom can write to OTP regions via the UART protocol, so it’s better thought of as controlled-access storage rather than truly write-once — on-the-fly flash encryption via a cache encryption engine, and a battery-backed key processing unit...
Running code in a PAX Credit Card Payment Machine (part1)
Disclaimer All procedures described here were done with public available stuff - No security flaws were actually explored here to get code execution. The processor swap technique does not bypass the tamper protections neither allow a fake machine to actually emit payments. Brazilian credit card payment machines usually are in state of the art regarding security measures. I remember once a Elavon employee told me that Brazil got all the first releases of payment machines and systems. When asked why, he said: frauds in Brazil are sophisticated enough, that if the system is secure enough to Brazil, it works for...
TPM 2.0: Extracting Bitlocker keys through SPI
The TPM 2.0, also known as Trusted Platform Module 2.0, is a hardware security feature embedded in many modern computers. Its purpose is to provide a secure way to store cryptographic keys and other sensitive data, such as passwords and digital certificates, aiming to protect against various security threats, including unauthorized access to a computer’s hardware and software. TPM 2.0 represents an evolution of the original TPM specification, developed by the Trusted Computing Group (TCG), and features additional capabilities and resources, such as support for additional cryptographic algorithms and the ability to store larger amounts of data. Good Things Currently,...
NAND Flash Memory Analysis and Decoding - Unveiling ECC Scattering in Unknown Devices
Exploring NAND Memories When in possession of a device whose internals one wishes to understand, accessing the content of the flash memory is not always straightforward. Due to the nature of NAND memories, an error correction algorithm is applied to all content, which can cause unintentional obfuscation of the content. Some manufacturers of processors that directly control NAND-type memories or developers of “protected” software choose to customize the way these algorithms function. In this article, we will explore the basic structure of flash memory, why error correction exists, and how to identify the scattering of the error correction algorithm used....